Site Leaked Raw Format Photography Collection #803
Access Now site leaked superior online playback. No recurring charges on our content platform. Immerse yourself in a huge library of shows put on display in flawless visuals, the ultimate choice for elite viewing admirers. With newly added videos, you’ll always be in the know. Find site leaked preferred streaming in amazing clarity for a highly fascinating experience. Get involved with our streaming center today to observe private first-class media with absolutely no charges, free to access. Get frequent new content and delve into an ocean of bespoke user media engineered for prime media followers. Don't pass up special videos—download fast now! Explore the pinnacle of site leaked exclusive user-generated videos with sharp focus and featured choices.
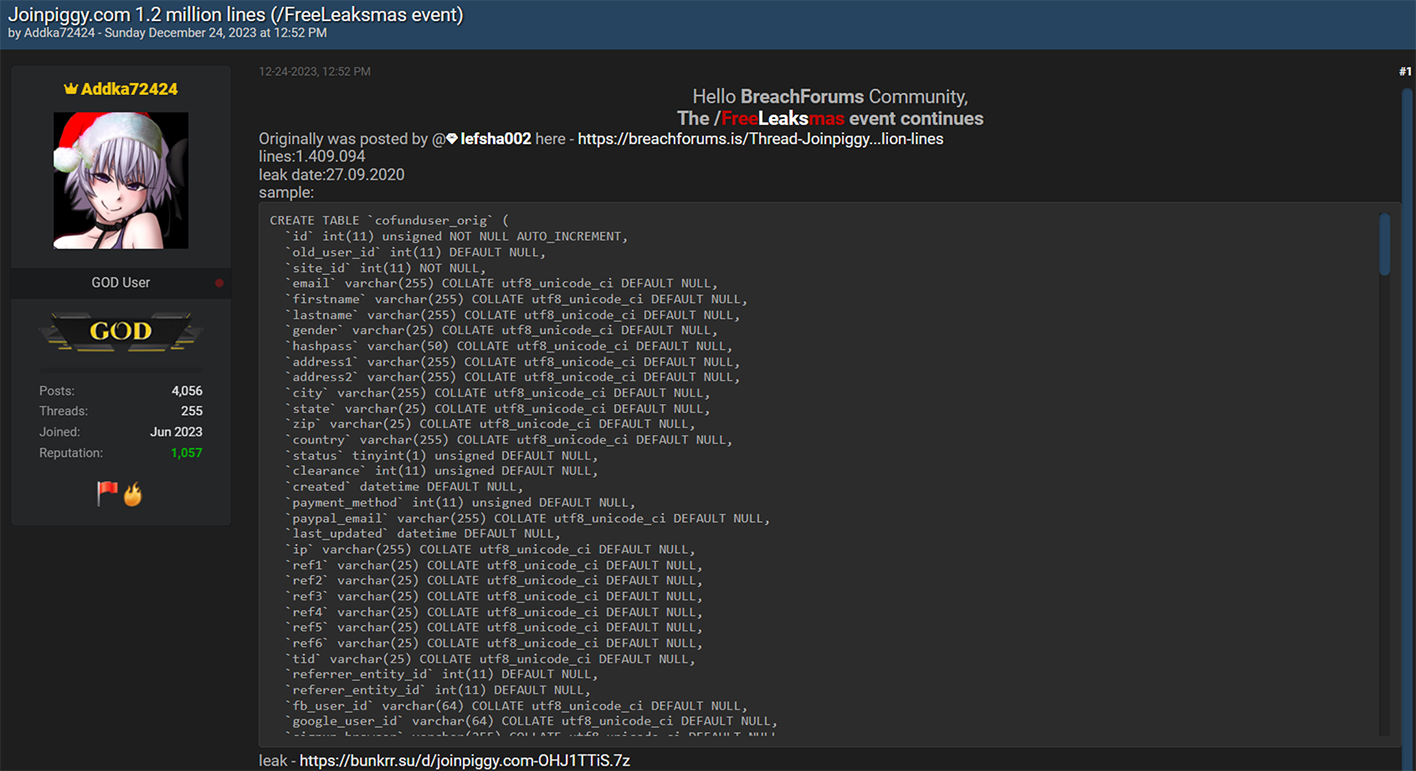
This email address has been found in multiple data breaches Stay updated on privacy breaches, security threats, and expert insights to protect your digital world. Review the details below to see where your data was exposed.
Resecurity | Cybercriminals launched “Leaksmas” event in the Dark Web exposing massive volumes
Find out if your personal information was compromised in data breaches Your hub for leaked sensitive data and cyber news Search your email on databreach.com to see where your data was leaked and learn how to protect yourself.
A modern personal asset search engine created for security analysts, journalists, security companies, and everyday people to help secure accounts and provide insight on compromised assets
Free breach alerts & breach notifications. Breach directory check if your email or username was compromised search over 18 billion publicly leaked records need api access? Leaked information includes user passwords for platforms including google, facebook and apple, the report says. Cyber criminals collect data leaks and crack leaked password information
Found passwords are used to login on other services and takeover your accounts Compromised accounts are used to steal money, information and to start ransomware attacks Cyber criminal at work we collect data leaks and stealer logs We extract and crack passwords.
This site simply searches online databases of compromised account information in an attempt to help you keep your accounts safe and secure
Browserleaks is a suite of tools that offers a range of tests to evaluate the security and privacy of your web browser These tests focus on identifying ways in which websites may leak your real ip address, collect information about your device, and perform a browser fingerprinting. Discover compromised data with osintleak, the ultimate search engine for dark web content, leaked databases, stealer logs, and sensitive information Ideal for cybersecurity professionals and investigators, osintleak offers advanced tools to search, analyze, and monitor exposed credentials and data breaches.